[index] AT-TQ6702 GEN2-R コマンドリファレンス 5.5.5
NoteダイナミックDNSサービスに障害が発生した場合、IPsec VPNの確立が行えない場合があります。信頼性が必要とされるネットワークでは、固定IPアドレス契約の利用をご検討ください。
Note検証済みダイナミックDNSサービスは弊社ホームページをご確認ください。
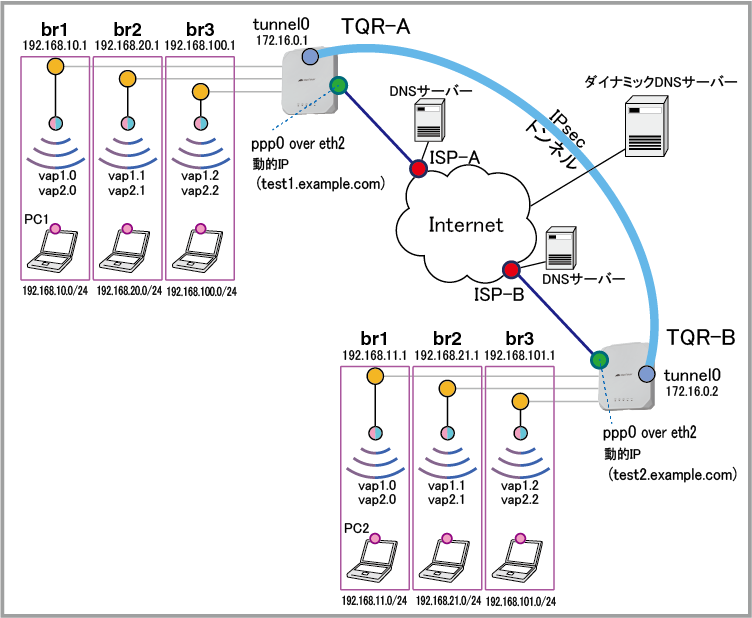
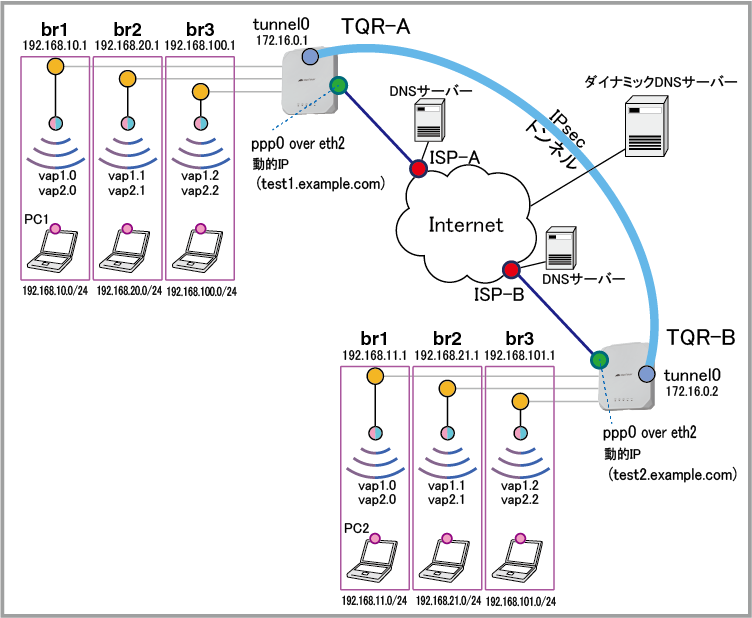
| vap1.0 | 無線1 (2.4GHz) VAP0 | Network2 | WPAパーソナル | passphrase1 | WPA2 WPA3 |
| vap1.1 | 無線1 (2.4GHz) VAP1 | Sales2 | WPAエンタープライズ | - | WPA3 |
| vap1.2 | 無線1 (2.4GHz) VAP2 | Management2 | WPAエンタープライズ | - | WPA3 |
| vap2.0 | 無線2 (5GHz) VAP0 | Network5 | WPAパーソナル | passphrase17 | WPA2 WPA3 |
| vap2.1 | 無線2 (5GHz) VAP1 | Sales5 | WPAエンタープライズ | - | WPA3 |
| vap2.2 | 無線2 (5GHz) VAP2 | Management5 | WPAエンタープライズ | - | WPA3 |
NoteVAPインターフェースの命名規則については「インターフェース」/「一般設定」をご参照ください。
| ISP接続用ユーザー名 | user@ispA | user@ispB |
| ISP接続用パスワード | isppasswdA | isppasswdB |
| PPPoEサービス名 | 指定なし | 指定なし |
| WAN側IPアドレス | 動的割り当て(IPCP) | 動的割り当て(IPCP) |
| DNSサーバー | 自動取得(IPCP) | 自動取得(IPCP) |
| 接続形態 | 端末型 | 端末型 |
| br1 | vap1.0 vap2.0 | vap1.0 vap2.0 |
| br2 | vap1.1 vap2.1 | vap1.1 vap2.1 |
| br3 | vap1.2 vap2.2 | vap1.2 vap2.2 |
| WAN側物理インターフェース | eth2 | eth2 |
| WAN側(ppp0)IPアドレス | 接続時にISP-Aから取得 | 接続時にISP-Bから取得 |
| LAN側(br1)IPアドレス | 192.168.10.1/24 | 192.168.11.1/24 |
| LAN側(br2)IPアドレス | 192.168.20.1/24 | 192.168.22.1/24 |
| LAN側(br3)IPアドレス | 192.168.100.1/24 | 192.168.101.1/24 |
| IKEバージョン | IKEv2 | IKEv2 |
| ローカルID | test1.example.com | test2.example.com |
| リモートID | test2.example.com | test1.example.com |
| サーバーのFQDN | members.example.com | members.example.com |
| サーバーのTCPポート番号 | 443 | 443 |
| サーバー接続用ユーザー名 | test | test |
| サーバー接続用パスワード | test | test |
| ホスト名 | test1.example.com | test2.example.com |
| IPアドレスを登録するインターフェース | ppp0 | ppp0 |
| リース時間 | 2時間 | 2時間 |
| 対象サブネット | 192.168.10.0/24 | 192.168.11.0/24 |
| デフォルトゲートウェイ | 192.168.10.1 | 192.168.11.1 |
| DNSサーバー | 192.168.10.1 | 192.168.11.1 |
| 提供するIPアドレスの範囲 | 192.168.10.100~192.168.10.131(32個) | 192.168.11.100~192.168.11.131(32個) |
| リース時間 | 2時間 | 2時間 |
| 対象サブネット | 192.168.20.0/24 | 192.168.21.0/24 |
| デフォルトゲートウェイ | 192.168.20.1 | 192.168.21.1 |
| DNSサーバー | 192.168.20.1 | 192.168.21.1 |
| 提供するIPアドレスの範囲 | 192.168.20.100~192.168.20.131(32個) | 192.168.21.100~192.168.21.131(32個) |
| リース時間 | 2時間 | 2時間 |
| 対象サブネット | 192.168.100.0/24 | 192.168.101.0/24 |
| デフォルトゲートウェイ | 192.168.100.1 | 192.168.101.1 |
| DNSサーバー | 192.168.100.1 | 192.168.101.1 |
| 提供するIPアドレスの範囲 | 192.168.100.100~192.168.100.131(32個) | 192.168.101.100~192.168.101.131(32個) |
NoteTQR-A、Bが使用するホスト名やダイナミックDNSサーバーにアクセスするためのアカウントは、あらかじめ取得してあるものとします。
ホスト名やアカウントの取得については、ダイナミックDNSサービスの利用開始手順をご覧ください。
wireless
security 1 mode wpa-personal key passphrase1 versions wpa2 wpa3 security 2 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 3 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 17 mode wpa-personal key passphrase17 versions wpa2 wpa3 security 18 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 19 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required
Note本設定例では、2.4GHzと5GHzのVAPに別々のSSIDを設定していますが、両帯域のVAPに同じSSIDを設定し、バンドステアリングを有効にすることで、2.4GHz・5GHz帯の両方をサポートしている無線端末に対し、混雑していない帯域への接続を促し、帯域を有効に使うことができます。
具体的な設定については設定例集#201aをご参照ください。
network 1 ssid Network2 hide-ssid security 1 network 2 ssid Sales2 hide-ssid security 2 network 3 ssid Management2 hide-ssid security 3 network 17 ssid Network5 hide-ssid security 17 network 18 ssid Sales5 hide-ssid security 18 network 19 ssid Management5 hide-ssid security 19
ap-profile local radio 1 enable vap 0 network 1 vap 1 network 2 vap 2 network 3 radio 2 enable zero-wait-dfs enable vap 0 network 17 vap 1 network 18 vap 2 network 19
radius-server local server enable nas 127.0.0.1 key awplus-local-radius-server user userA password passwdA user userB password passwdB user userC password passwdC
radius-server host 127.0.0.1 key awplus-local-radius-server
end wireless ap-configuration apply ap local configure terminal
bridge 1 bridge 2 bridge 3
Note本設定例では、2.4GHzと5GHzの同一番号のVAPをブリッジに所属させ同じセグメントで運用しています。
2.4GHzと5GHzのVAPを異なるセグメントで運用する場合は、VAPごとにブリッジを用意して(本例ではブリッジを6つ作成して)、各ブリッジにIPアドレスを設定し、エンティティーとファイアウォールの設定を変更してください。
interface vap1.0 bridge-group 1 interface vap1.1 bridge-group 2 interface vap1.2 bridge-group 3 interface vap2.0 bridge-group 1 interface vap2.1 bridge-group 2 interface vap2.2 bridge-group 3
end wireless ap-configuration apply ap local configure terminal
ddns enable
?」をCLIから入力するには、Ctrl/V キーを入力してから ? を入力してください。単に ? を入力するとCLIヘルプが表示されてしまうためご注意ください。ddns-update-method example update-url https://<USERNAME>:<PASSWORD>@members.example.com/nic/update?SYSTEM=dyndns&hostname=<HOST-NAME>&myip=<IPADDRESS> host-name test1.example.com username test password test update-interval 60 retry-interval 1 maximum-retries 5
interface eth2 encapsulation ppp 0
interface ppp0 ip ddns-update-method example ppp ipcp dns request keepalive ip address negotiated ppp username user@ispA ppp password isppasswdA ip tcp adjust-mss pmtu
interface br1 ip address 192.168.10.1/24 interface br2 ip address 192.168.20.1/24 interface br3 ip address 192.168.100.1/24
zone private network lan1 ip subnet 192.168.10.0/24 network lan2 ip subnet 192.168.20.0/24 network lan3 ip subnet 192.168.100.0/24 network peer1 ip subnet 192.168.11.0/24 interface tunnel0 network peer2 ip subnet 192.168.21.0/24 interface tunnel0 network peer3 ip subnet 192.168.101.0/24 interface tunnel0 network tunnel ip subnet 172.16.0.0/30
zone public network wan ip subnet 0.0.0.0/0 interface ppp0 host ppp0 ip address dynamic interface ppp0
application esp protocol 50
application isakmp protocol udp sport 500 dport 500
firewall rule 10 permit any from private to private rule 20 permit any from private to public rule 30 permit isakmp from public.wan.ppp0 to public.wan rule 40 permit isakmp from public.wan to public.wan.ppp0 rule 50 permit esp from public.wan.ppp0 to public.wan rule 60 permit esp from public.wan to public.wan.ppp0 rule 70 permit dns from public.wan.ppp0 to public.wan rule 80 permit https from public.wan.ppp0 to public.wan protect
nat rule 10 masq any from private to public enable
ip dhcp pool pool10 network 192.168.10.0 255.255.255.0 range 192.168.10.100 192.168.10.131 dns-server 192.168.10.1 default-router 192.168.10.1 lease 0 2 0 ip dhcp pool pool20 network 192.168.20.0 255.255.255.0 range 192.168.20.100 192.168.20.131 dns-server 192.168.20.1 default-router 192.168.20.1 lease 0 2 0 ip dhcp pool pool100 network 192.168.100.0 255.255.255.0 range 192.168.100.100 192.168.100.131 dns-server 192.168.100.1 default-router 192.168.100.1 lease 0 2 0
service dhcp-server
crypto isakmp key secret hostname test2.example.com
interface tunnel0 mtu 1300 tunnel source ppp0 tunnel destination test2.example.com tunnel local name test1.example.com tunnel remote name test2.example.com tunnel protection ipsec tunnel mode ipsec ipv4 ip address 172.16.0.1/30 ip tcp adjust-mss 1260
ping-poll 1 ip 172.16.0.2 active
trigger 1 type ping-poll 1 down script 1 periodic-update.scp trigger 2 type ping-poll 1 up script 1 periodic-update-delete.scp trigger 3 type periodic 1 script 1 host-change.scp
ip route 0.0.0.0/0 ppp0 ip route 192.168.11.0/24 tunnel0 ip route 192.168.11.0/24 null 254 ip route 192.168.21.0/24 tunnel0 ip route 192.168.21.0/24 null 254 ip route 192.168.101.0/24 tunnel0 ip route 192.168.101.0/24 null 254
ip dns forwarding
end
wireless
security 1 mode wpa-personal key passphrase1 versions wpa2 wpa3 security 2 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 3 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 17 mode wpa-personal key passphrase17 versions wpa2 wpa3 security 18 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 19 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required
Note本設定例では、2.4GHzと5GHzのVAPに別々のSSIDを設定していますが、両帯域のVAPに同じSSIDを設定し、バンドステアリングを有効にすることで、2.4GHz・5GHz帯の両方をサポートしている無線端末に対し、混雑していない帯域への接続を促し、帯域を有効に使うことができます。
具体的な設定については設定例集#201aをご参照ください。
network 1 ssid Network2 hide-ssid security 1 network 2 ssid Sales2 hide-ssid security 2 network 3 ssid Management2 hide-ssid security 3 network 17 ssid Network5 hide-ssid security 17 network 18 ssid Sales5 hide-ssid security 18 network 19 ssid Management5 hide-ssid security 19
ap-profile local radio 1 enable vap 0 network 1 vap 1 network 2 vap 2 network 3 radio 2 enable zero-wait-dfs enable vap 0 network 17 vap 1 network 18 vap 2 network 19
radius-server local server enable nas 127.0.0.1 key awplus-local-radius-server user userA password passwdA user userB password passwdB user userC password passwdC
radius-server host 127.0.0.1 key awplus-local-radius-server
end wireless ap-configuration apply ap local configure terminal
bridge 1 bridge 2 bridge 3
Note本設定例では、2.4GHzと5GHzの同一番号のVAPをブリッジに所属させ同じセグメントで運用しています。
2.4GHzと5GHzのVAPを異なるセグメントで運用する場合は、VAPごとにブリッジを用意して(本例ではブリッジを6つ作成して)、各ブリッジにIPアドレスを設定し、エンティティーとファイアウォールの設定を変更してください。
interface vap1.0 bridge-group 1 interface vap1.1 bridge-group 2 interface vap1.2 bridge-group 3 interface vap2.0 bridge-group 1 interface vap2.1 bridge-group 2 interface vap2.2 bridge-group 3
end wireless ap-configuration apply ap local configure terminal
ddns enable
?」をCLIから入力するには、Ctrl/V キーを入力してから ? を入力してください。単に ? を入力するとCLIヘルプが表示されてしまうためご注意ください。ddns-update-method example update-url https://<USERNAME>:<PASSWORD>@members.example.com/nic/update?SYSTEM=dyndns&hostname=<HOST-NAME>&myip=<IPADDRESS> host-name test2.example.com username test password test update-interval 60 retry-interval 10 maximum-retries 5
interface eth2 encapsulation ppp 0
interface ppp0 ip ddns-update-method example ppp ipcp dns request keepalive ip address negotiated ppp username user@isp2 ppp password isppasswd2 ip tcp adjust-mss pmtu
interface br1 ip address 192.168.11.1/24 interface br2 ip address 192.168.21.1/24 interface br3 ip address 192.168.101.1/24
zone private network lan1 ip subnet 192.168.11.0/24 network lan2 ip subnet 192.168.21.0/24 network lan3 ip subnet 192.168.101.0/24 network peer1 ip subnet 192.168.10.0/24 interface tunnel0 network peer2 ip subnet 192.168.20.0/24 interface tunnel0 network peer3 ip subnet 192.168.100.0/24 interface tunnel0 network tunnel ip subnet 172.16.0.0/30
zone public network wan ip subnet 0.0.0.0/0 interface ppp0 host ppp0 ip address dynamic interface ppp0
application esp protocol 50
application isakmp protocol udp sport 500 dport 500
firewall rule 10 permit any from private to private rule 20 permit any from private to public rule 30 permit isakmp from public.wan.ppp0 to public.wan rule 40 permit isakmp from public.wan to public.wan.ppp0 rule 50 permit esp from public.wan.ppp0 to public.wan rule 60 permit esp from public.wan to public.wan.ppp0 rule 70 permit dns from public.wan.ppp0 to public.wan rule 80 permit https from public.wan.ppp0 to public.wan protect
nat rule 10 masq any from private to public enable
ip dhcp pool pool11 network 192.168.11.0 255.255.255.0 range 192.168.11.100 192.168.11.131 dns-server 192.168.11.1 default-router 192.168.11.1 lease 0 2 0 ip dhcp pool pool21 network 192.168.21.0 255.255.255.0 range 192.168.21.100 192.168.21.131 dns-server 192.168.21.1 default-router 192.168.21.1 lease 0 2 0 ip dhcp pool pool101 network 192.168.101.0 255.255.255.0 range 192.168.101.100 192.168.101.131 dns-server 192.168.101.1 default-router 192.168.101.1 lease 0 2 0
service dhcp-server
crypto isakmp key secret hostname test1.example.com
interface tunnel0 mtu 1300 tunnel source ppp0 tunnel destination test1.example.com tunnel local name test2.example.com tunnel remote name test1.example.com tunnel protection ipsec tunnel mode ipsec ipv4 ip address 172.16.0.2/30 ip tcp adjust-mss 1260
ping-poll 1 ip 172.16.0.1 active
trigger 1 type ping-poll 1 down script 1 periodic-update.scp trigger 2 type ping-poll 1 up script 1 periodic-update-delete.scp trigger 3 type periodic 1 script 1 host-change.scp
ip route 0.0.0.0/0 ppp0 ip route 192.168.10.0/24 tunnel0 ip route 192.168.10.0/24 null 254 ip route 192.168.20.0/24 tunnel0 ip route 192.168.20.0/24 null 254 ip route 192.168.100.0/24 tunnel0 ip route 192.168.100.0/24 null 254
ip dns forwarding
end
copy running-config startup-config」の書式で実行します。awplus# copy running-config startup-config ↓ Building configuration... [OK]
awplus# write memory ↓ Building configuration... [OK]
awplus(config)# log buffered level informational facility local5 ↓
awplus# show log | include Firewall ↓
! wireless ! security 1 mode wpa-personal key passphrase1 versions wpa2 wpa3 security 2 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 3 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 17 mode wpa-personal key passphrase17 versions wpa2 wpa3 security 18 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 19 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required ! network 1 ssid Network2 hide-ssid security 1 network 2 ssid Sales2 hide-ssid security 2 network 3 ssid Management2 hide-ssid security 3 network 17 ssid Network5 hide-ssid security 17 network 18 ssid Sales5 hide-ssid security 18 network 19 ssid Management5 hide-ssid security 19 ! ap-profile local radio 1 enable vap 0 network 1 vap 1 network 2 vap 2 network 3 radio 2 enable zero-wait-dfs enable vap 0 network 17 vap 1 network 18 vap 2 network 19 ! radius-server local server enable nas 127.0.0.1 key awplus-local-radius-server user userA password passwdA user userB password passwdB user userC password passwdC ! radius-server host 127.0.0.1 key awplus-local-radius-server ! bridge 1 bridge 2 bridge 3 ! interface vap1.0 bridge-group 1 interface vap1.1 bridge-group 2 interface vap1.2 bridge-group 3 interface vap2.0 bridge-group 1 interface vap2.1 bridge-group 2 interface vap2.2 bridge-group 3 ! ddns enable ! ddns-update-method example update-url https://<USERNAME>:<PASSWORD>@members.example.com/nic/update?SYSTEM=dyndns&hostname=<HOST-NAME>&myip=<IPADDRESS> host-name test1.example.com username test password test update-interval 60 retry-interval 1 maximum-retries 5 ! interface eth2 encapsulation ppp 0 ! interface ppp0 ip ddns-update-method example ppp ipcp dns request keepalive ip address negotiated ppp username user@ispA ppp password isppasswdA ip tcp adjust-mss pmtu ! interface br1 ip address 192.168.10.1/24 interface br2 ip address 192.168.20.1/24 interface br3 ip address 192.168.100.1/24 ! zone private network lan1 ip subnet 192.168.10.0/24 network lan2 ip subnet 192.168.20.0/24 network lan3 ip subnet 192.168.100.0/24 network peer1 ip subnet 192.168.11.0/24 interface tunnel0 network peer2 ip subnet 192.168.21.0/24 interface tunnel0 network peer3 ip subnet 192.168.101.0/24 interface tunnel0 network tunnel ip subnet 172.16.0.0/30 ! zone public network wan ip subnet 0.0.0.0/0 interface ppp0 host ppp0 ip address dynamic interface ppp0 ! application esp protocol 50 ! application isakmp protocol udp sport 500 dport 500 ! firewall rule 10 permit any from private to private rule 20 permit any from private to public rule 30 permit isakmp from public.wan.ppp0 to public.wan rule 40 permit isakmp from public.wan to public.wan.ppp0 rule 50 permit esp from public.wan.ppp0 to public.wan rule 60 permit esp from public.wan to public.wan.ppp0 rule 70 permit dns from public.wan.ppp0 to public.wan rule 80 permit https from public.wan.ppp0 to public.wan protect ! nat rule 10 masq any from private to public enable ! ip dhcp pool pool10 network 192.168.10.0 255.255.255.0 range 192.168.10.100 192.168.10.131 dns-server 192.168.10.1 default-router 192.168.10.1 lease 0 2 0 ip dhcp pool pool20 network 192.168.20.0 255.255.255.0 range 192.168.20.100 192.168.20.131 dns-server 192.168.20.1 default-router 192.168.20.1 lease 0 2 0 ip dhcp pool pool100 network 192.168.100.0 255.255.255.0 range 192.168.100.100 192.168.100.131 dns-server 192.168.100.1 default-router 192.168.100.1 lease 0 2 0 ! service dhcp-server ! crypto isakmp key secret hostname test2.example.com ! interface tunnel0 mtu 1300 tunnel source ppp0 tunnel destination test2.example.com tunnel local name test1.example.com tunnel remote name test2.example.com tunnel protection ipsec tunnel mode ipsec ipv4 ip address 172.16.0.1/30 ip tcp adjust-mss 1260 ! ping-poll 1 ip 172.16.0.2 active ! trigger 1 type ping-poll 1 down script 1 periodic-update.scp trigger 2 type ping-poll 1 up script 1 periodic-update-delete.scp trigger 3 type periodic 1 script 1 host-change.scp ! ip route 0.0.0.0/0 ppp0 ip route 192.168.11.0/24 tunnel0 ip route 192.168.11.0/24 null 254 ip route 192.168.21.0/24 tunnel0 ip route 192.168.21.0/24 null 254 ip route 192.168.101.0/24 tunnel0 ip route 192.168.101.0/24 null 254 ! ip dns forwarding ! end
! wireless ! security 1 mode wpa-personal key passphrase1 versions wpa2 wpa3 security 2 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 3 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 17 mode wpa-personal key passphrase17 versions wpa2 wpa3 security 18 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required security 19 mode wpa-enterprise versions wpa3 radius authentication group radius management-frame-protection enable type required ! network 1 ssid Network2 hide-ssid security 1 network 2 ssid Sales2 hide-ssid security 2 network 3 ssid Management2 hide-ssid security 3 network 17 ssid Network5 hide-ssid security 17 network 18 ssid Sales5 hide-ssid security 18 network 19 ssid Management5 hide-ssid security 19 ! ap-profile local radio 1 enable vap 0 network 1 vap 1 network 2 vap 2 network 3 radio 2 enable zero-wait-dfs enable vap 0 network 17 vap 1 network 18 vap 2 network 19 ! radius-server local server enable nas 127.0.0.1 key awplus-local-radius-server user userA password passwdA user userB password passwdB user userC password passwdC ! radius-server host 127.0.0.1 key awplus-local-radius-server ! bridge 1 bridge 2 bridge 3 ! interface vap1.0 bridge-group 1 interface vap1.1 bridge-group 2 interface vap1.2 bridge-group 3 interface vap2.0 bridge-group 1 interface vap2.1 bridge-group 2 interface vap2.2 bridge-group 3 ! ddns enable ! ddns-update-method example update-url https://<USERNAME>:<PASSWORD>@members.example.com/nic/update?SYSTEM=dyndns&hostname=<HOST-NAME>&myip=<IPADDRESS> host-name test2.example.com username test password test update-interval 60 retry-interval 10 maximum-retries 5 ! interface eth2 encapsulation ppp 0 ! interface ppp0 ip ddns-update-method example ppp ipcp dns request keepalive ip address negotiated ppp username user@isp2 ppp password isppasswd2 ip tcp adjust-mss pmtu ! interface br1 ip address 192.168.11.1/24 interface br2 ip address 192.168.21.1/24 interface br3 ip address 192.168.101.1/24 ! zone private network lan1 ip subnet 192.168.11.0/24 network lan2 ip subnet 192.168.21.0/24 network lan3 ip subnet 192.168.101.0/24 network peer1 ip subnet 192.168.10.0/24 interface tunnel0 network peer2 ip subnet 192.168.20.0/24 interface tunnel0 network peer3 ip subnet 192.168.100.0/24 interface tunnel0 network tunnel ip subnet 172.16.0.0/30 ! zone public network wan ip subnet 0.0.0.0/0 interface ppp0 host ppp0 ip address dynamic interface ppp0 ! application esp protocol 50 ! application isakmp protocol udp sport 500 dport 500 ! firewall rule 10 permit any from private to private rule 20 permit any from private to public rule 30 permit isakmp from public.wan.ppp0 to public.wan rule 40 permit isakmp from public.wan to public.wan.ppp0 rule 50 permit esp from public.wan.ppp0 to public.wan rule 60 permit esp from public.wan to public.wan.ppp0 rule 70 permit dns from public.wan.ppp0 to public.wan rule 80 permit https from public.wan.ppp0 to public.wan protect ! nat rule 10 masq any from private to public enable ! ip dhcp pool pool11 network 192.168.11.0 255.255.255.0 range 192.168.11.100 192.168.11.131 dns-server 192.168.11.1 default-router 192.168.11.1 lease 0 2 0 ip dhcp pool pool21 network 192.168.21.0 255.255.255.0 range 192.168.21.100 192.168.21.131 dns-server 192.168.21.1 default-router 192.168.21.1 lease 0 2 0 ip dhcp pool pool101 network 192.168.101.0 255.255.255.0 range 192.168.101.100 192.168.101.131 dns-server 192.168.101.1 default-router 192.168.101.1 lease 0 2 0 ! service dhcp-server ! crypto isakmp key secret hostname test1.example.com ! interface tunnel0 mtu 1300 tunnel source ppp0 tunnel destination test1.example.com tunnel local name test2.example.com tunnel remote name test1.example.com tunnel protection ipsec tunnel mode ipsec ipv4 ip address 172.16.0.2/30 ip tcp adjust-mss 1260 ! ping-poll 1 ip 172.16.0.1 active ! trigger 1 type ping-poll 1 down script 1 periodic-update.scp trigger 2 type ping-poll 1 up script 1 periodic-update-delete.scp trigger 3 type periodic 1 script 1 host-change.scp ! ip route 0.0.0.0/0 ppp0 ip route 192.168.10.0/24 tunnel0 ip route 192.168.10.0/24 null 254 ip route 192.168.20.0/24 tunnel0 ip route 192.168.20.0/24 null 254 ip route 192.168.100.0/24 tunnel0 ip route 192.168.100.0/24 null 254 ! ip dns forwarding ! end
enable con t trigger 3 active end
enable con t trigger 3 no active end
enable clear isakmp sa peer test2.example.com force con t int tunnel0 tunnel destination test2.example.com end
enable con t trigger 3 active end
enable con t trigger 3 no active end
enable clear isakmp sa peer test1.example.com force con t int tunnel0 tunnel destination test1.example.com end
(C) 2023 - 2025 アライドテレシスホールディングス株式会社
PN: 613-003212 Rev.K